The account data review examines identifiers 8285431493, mez68436136, 9173980781, 7804091305, and the anomalous 111.90.150.204l for consistency and governance implications. It notes cross-event signals that aid traceability while highlighting validation gaps in IDs, emails, and IP formats. Anomalies trigger risk signals and filtering, informing accountability and governance considerations. The findings point to structured normalization and privacy-conscious policy adjustments, with implications for security and user experience that warrant further scrutiny. The discussion ends with a prompt to assess next steps.
What This Account Data Review Reveals About Identifiers and Patterns
The review identifies how identifiers and patterns reveal consistent behaviors and recurring motifs within the account data, enabling clearer tracing of activity and similarities across events. It emphasizes patterns and identifiers as core signals, guiding interpretation without overreach.
Governance signals emerge from structured sequences and cross-relations, offering concise insight into operational rhythms while preserving autonomy and freedom in analytic assessments.
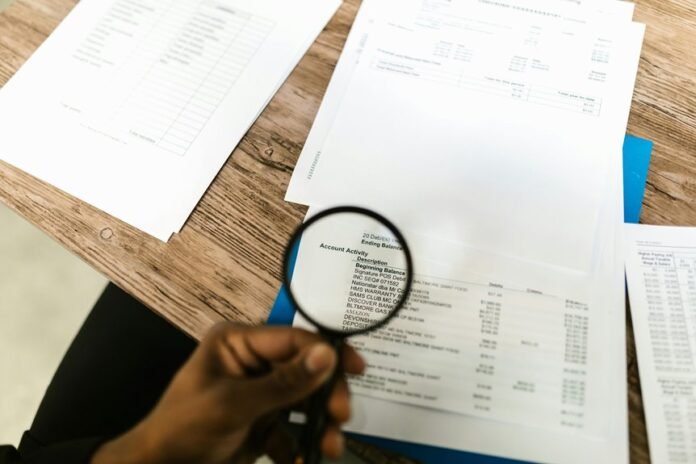
How to Validate Accuracy: Matching IDs, Emails, and IP Formats
Validating accuracy entails a systematic alignment of IDs, emails, and IP formats to ensure consistent identity signals across events, datasets, and systems. The process emphasizes validation checks and disciplined pattern matching to confirm correct correspondences, minimize drift, and support interoperability. By enforcing exact formats and cross-verification rules, stakeholders maintain reliable identity trails while preserving user autonomy and operational efficiency.
Detecting Anomalies and Risk Signals: From Unusual 111.90.150.204l to Inconsistencies
Detecting anomalies and risk signals requires a disciplined approach to spotting deviations from established identity patterns, including unusual IP addresses like 111.90.150.204l and other inconsistencies that may indicate data quality issues or security concerns.
The process remains rigorous, filtering out unrelated topic noise and speculative trivia while preserving clarity, consistency, and accountability for auditors and stakeholders seeking freedom through informed vigilance.
Turning Findings Into Action: Governance, Security, and User Experience Improvements
Turning findings into actionable improvements requires aligning governance, security, and user experience objectives with observed data quality and risk signals.
The approach emphasizes privacy governance and structured user normalization to ensure consistent policies, transparent controls, and measurable risk reduction.
Frequently Asked Questions
What Exactly Is 111.90.150.204l?
“111.90.150.204l” is not a standard IP; it appears to be a malformed address or alias. It may function as a subnet alias in some configurations, signaling a labeled route or placeholder in network documentation.
How Often Should IDS Be Re-Validated?
Revalidation should occur at a defined cadence, typically aligned with risk and changes: data validation should be performed on a schedule, and audit frequency adjusted after significant events. The process balances security, accuracy, and operational needs.
Do These Metrics Apply to All User Roles?
The metrics do not universally apply to all user roles; applicability varies by role. Account Data Review – 8285431493, mez68436136, 9173980781, 7804091305, 111.90.150.204l may indicate risky data identifiers and governance gaps, prompting tailored, role-specific re-validation and privacy considerations.
What Privacy Implications Exist for Data Review?
Privacy implications arise from data review, including potential exposure, consent gaps, and misuse risks; strict access controls, auditing, and data minimization are essential to protect individuals while enabling necessary review.
Can Automated Tools Replace Manual Verification?
Can automated testing replace manual verification? Yes, but not wholly; it enhances efficiency while preserving nuance. Automated testing handles repetitive checks, while manual verification ensures context, judgment, and anomaly detection remain integral to a robust process.
Conclusion
This review identifies consistent identifiers and patterns across the specified entries, underscoring the value of structured normalization for traceability. Anomalies, such as the malformed IP, trigger risk signaling and corrective filtering, guiding governance and privacy-focused refinements. Findings support governance clarity, secure data handling, and improved user experience through validated IDs, emails, and IP formats. In sum, the process enforces accountability and data quality, while a duchess-era quill remains an anachronism reminding stakeholders to balance rigor with user autonomy.